Memory Regions of a Process When studying dynamic memory management in C/C++, we often categorize the address space into several logical regions: stack, heap, data segment (BSS, initialized data), and text (code). However, these addresses are not physical memory addresses. Consider the following exa...
Real-Time File Searching with findThe find command performs an exhaustive, real-time traversal of the filesystem hierarchy, evaluating files based on specified criteria.Search CriteriaName Matching: -name for case-sensitive matches and -iname for case-insensitive matches.find /usr/local -name "*.cfg...
1. Gateway Server and Host Configuration Set up gateway server with dual NICs: ens36: 12.0.0.254/24, ens33: 192.168.241.254/24. Server1 uses 192.168.241.0/24. PC1 and Server2 obtain IP via DHCP. Enable remote SSH access (e.g., Xshell) to Server1 and the gateway. Adjusting Network Interfaces On the g...
Simulating Filesystem Constraints and Loop Device Mounts A basic loop device can be created and mounted to create a space-restricted test environment: # Create a 100K file and associate it with a loop device # Then mount it at /app/log dd if=/dev/zero of=/tmp/100k bs=1K count=100 losetup /dev/loop0...
AWK Syntax and FundamentalsAWK functions as a pattern scanning and processing language. It interprets data as a series of records (lines) and fields (columns). The default separator is whitespace. The general execution flow follows awk 'pattern { action }' filename. If a pattern evaluates to true, t...
Installing Redis from Source on Linux To install Redis on distributions like CentOS 7 or Ubuntu 18.04: Download the source archive: wget http://download.redis.io/releases/redis-4.0.0.tar.gz Extract the archive: tar -xvf redis-4.0.0.tar.gz Compile the source: cd redis-4.0.0 make If compilation fails...
Distributing incoming network traffic across multiple backend servers mitigates single-point bottlenecks, enhances bandwidth capacity, and ensures continuous service availability. When individual nodes exceed their processing thresholds, clustering mechanisms route requests simultaneously. This arch...
System calls operate as the strict enforcement boundary between unprivileged user applications and privileged kernel operations. When an application requires hardware access, memory management, or scheduling services, it cannot execute these instructions directly. Instead, it triggers a controlled t...
epoll is a scalable I/O event notification mechanism in the Linux kernel, widely used by high-performance systems like Nginx, Redis, and Netty. Its design overcomes fundamental limitations of older approaches such as select and poll, enabling efficient handling of tens or even millions of concurrent...
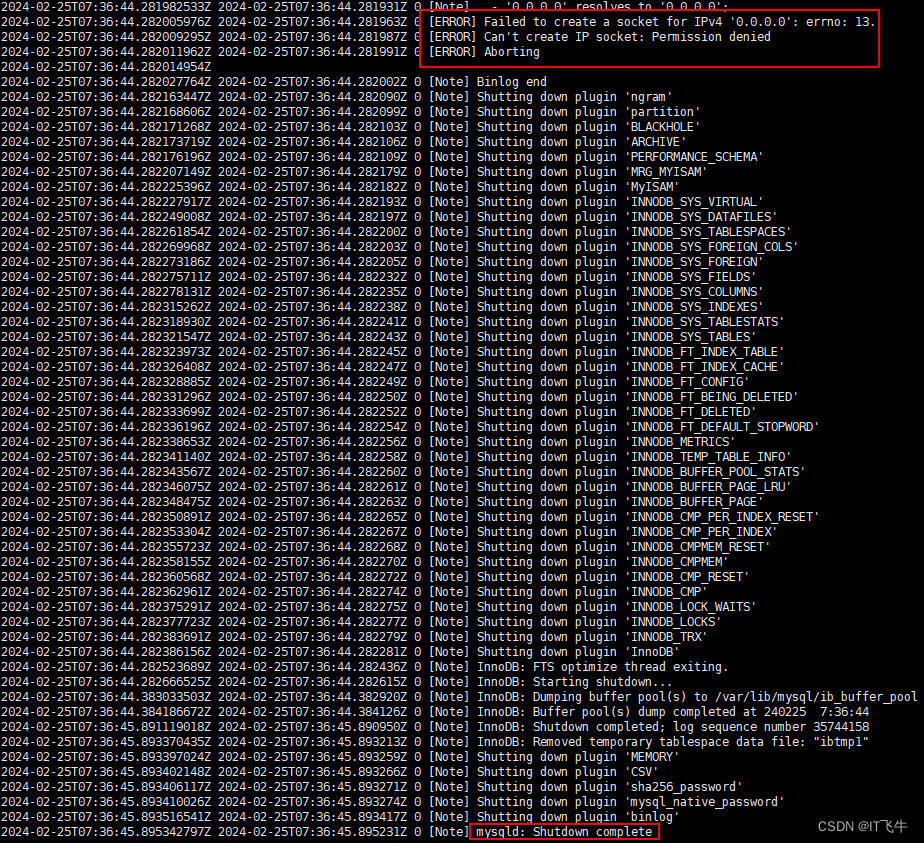
Analysis On an Ubuntu 20 server, a MySQL container based on Docker had been running stably. However, after installing Apache2 and MySQL directly via apt on Linux, restarting the MySQL container failed. When encountering a problem, first check the container's error logs. Execute the log view command:...