Venus CTF Walkthrough: Missions 1-50 from HackMyVM
Introduction
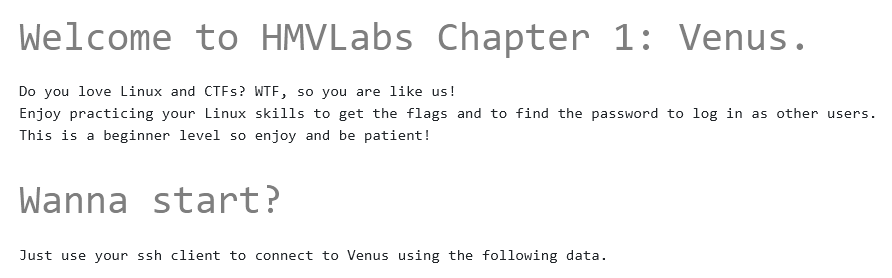
The Venus VM is suitable for beginners starting CTF and wanting to practice Linux skills.
- Target URL: https://hackmyvm.eu/venus/
- There are 50 missions, submitting these 50 flags counts as completion. (Currently, the top-ranked player has submitted 58 flags.)
Login:
ssh hacker@venus.hackmyvm.eu -p 5000
havefun!
0x01 Hidden Files
~$ cat mission.txt
################
# MISSION 0x01 #
################
## EN ##
User sophia has saved her password in a hidden file in this folder. Find it and log in as sophia.
## ES ##
La usuaria sophia ha guardado su contraseña en un fichero oculto en esta carpeta.Encuentralo y logueate como sophia.
List hidden files:
ls -al
Switch user:
su - username
# The dash switches both the working directory and environment.
0x02 Find by Filename
~$ cat mission.txt
################
# MISSION 0x02 #
################
## EN ##
The user angela has saved her password in a file but she does not remember where ... she only remembers that the file was called whereismypazz.txt
## ES ##
La usuaria angela ha guardado su password en un fichero pero no recuerda donde... solo recuerda que el fichero se llamaba whereismypazz.txt
Find file by name:
find / -name whereismypazz.txt -type f 2>/dev/null
0x03 File at Specific Line Number
~$ ls
findme.txt flagz.txt mission.txt
~$ cat mission.txt
################
# MISSION 0x03 #
################
## EN ##
The password of the user emma is in line 4069 of the file findme.txt
## ES ##
La password de la usuaria emma esta en la linea 4069 del fichero findme.txt
Output line 4069:
cat -n findme.txt | grep 4069
0x04 Filename is -
~$ ls
- flagz.txt mission.txt
~$ cat mission.txt
################
# MISSION 0x04 #
################
## EN ##
User mia has left her password in the file -.
## ES ##
La usuaria mia ha dejado su password en el fichero -.
Read file named -:
cat ./-
0x05 Find by Folder Name
~$ cat mission.txt
################
# MISSION 0x05 #
################
## EN ##
It seems that the user camila has left her password inside a folder called hereiam
## ES ##
Parece que la usuaria camila ha dejado su password dentro de una carpeta llamada hereiam
Find folder by name:
find / -name 'hereiam' -type d 2>/dev/null
0x06 Find by File Type
~$ ls
flagz.txt mission.txt muack
~$ cat mission.txt
################
# MISSION 0x06 #
################
## EN ##
The user luna has left her password in a file inside the muack folder.
## ES ##
La usuaria luna ha dejado su password en algun fichero dentro de la carpeta muack.
The password is in side the muack folder:
~$ ls muack
1 123 148 172 197 220 245 27 294 318 342 367 391 415 44 464 489 512 537 67 91
10 124 149 173 198 221 246 270 295 319 343 368 392 416 440 465 49 513 538 68 92
100 125 15 174 199 222 247 271 296 32 344 369 393
It's a nested folder. Find files:
find muack -type f
Combine with cat:
find muack/ -type f -exec cat {} \;
0x07 Find by File Size
~$ cat mission.txt
################
# MISSION 0x07 #
################
## EN ##
The user eleanor has left her password in a file that occupies 6969 bytes.
## ES ##
La usuaria eleanor ha dejado su password en un fichero que ocupa 6969 bytes.
Find file by size:
find / -size 6969c -type f 2>/dev/null
# 'c' denotes bytes
0x08 Find by File Owner
~$ cat mission.txt
################
# MISSION 0x08 #
################
## EN ##
The user victoria has left her password in a file in which the owner is the user violin.
## ES ##
La usuaria victoria ha dejado su password en un fichero en el cual el propietario es el usuario violin.
Find files owned by user violin:
find / -type f -user violin 2>/dev/null
0x09 Unzip ZIP
~$ ls
flagz.txt mission.txt passw0rd.zip
~$ cat mission.txt
################
# MISSION 0x09 #
################
## EN ##
The user isla has left her password in a zip file.
## ES ##
La usuaria isla ha dejado su password en un fichero zip.
Unzip the archive:
~$ unzip passw0rd.zip
Archive: passw0rd.zip
checkdir error: cannot create pwned
Permission denied
unable to process pwned/victoria/passw0rd.txt.
~$ unzip passw0rd.zip -d /tmp
# Extract to specified directory
0x10 Find Lines Starting with Specific Pattern
~$ ls
flagz.txt mission.txt passy
~$ cat mission.txt
################
# MISSION 0x10 #
################
## EN ##
The password of the user violet is in the line that begins with a9HFX (these 5 characters are not part of her password.).
## ES ##
El password de la usuaria violet esta en la linea que empieza por a9HFX (sin ser estos 5 caracteres parte de su password.).
Find lines starting with a9HFX:
grep ^a9HFX passy
0x11 Find Lines Ending with Specific Pattern
~$ ls
end flagz.txt mission.txt
~$ cat mission.txt
################
# MISSION 0x11 #
################
## EN ##
The password of the user lucy is in the line that ends with 0JuAZ (these last 5 characters are not part of her password)
## ES ##
El password de la usuaria lucy se encuentra en la linea que acaba por 0JuAZ (sin ser estos ultimos 5 caracteres parte de su password)
Find lines ending with 0JuAZ:
grep 0JuAZ$ end
0x12 Find String Between Two Patterns
~$ ls
file.yo flagz.txt mission.txt
~$ cat mission.txt
################
# MISSION 0x12 #
################
## EN ##
The password of the user elena is between the characters fu and ck
## ES ##
El password de la usuaria elena esta entre los caracteres fu y ck
Find content between fu and ck:
grep ^fu.*ck$ file.yo
0x13 Check Environment Variables
~$ cat mission.txt
################
# MISSION 0x13 #
################
## EN ##
The user alice has her password is in an environment variable.
## ES ##
La password de alice esta en una variable de entorno.
Check environment variables:
export
# or
printenv
0x14 /etc/passwd Comments
~$ cat mission.txt
################
# MISSION 0x14 #
################
## EN ##
The admin has left the password of the user anna as a comment in the file passwd.
## ES ##
El admin ha dejado la password de anna como comentario en el fichero passwd.
Check passwd file:
grep alice /etc/passwd
0x15 Sudo Privilege Escalation
~$ cat mission.txt
################
# MISSION 0x15 #
################
## EN ##
Maybe sudo can help you to be natalia.
## ES ##
Puede que sudo te ayude para ser natalia.
Hint that anna has sudo privileges:
~$ sudo -l
Matching Defaults entries for anna on venus:
env_reset, mail_badpass,
secure_path=/usr/local/sbin\:/usr/local/bin\:/usr/sbin\:/usr/bin\:/sbin\:/bin
User anna may run the following commands on venus:
(natalia) NOPASSWD: /bin/bash
:~$ sudo -u natalia /bin/bash
# or
sudo -u natalia -i
0x16 Base64 Decode
~$ ls
base64.txt flagz.txt mission.txt nataliapass.txt
~$ cat mission.txt
################
# MISSION 0x16 #
################
## EN ##
The password of user eva is encoded in the base64.txt file
## ES ##
El password de eva esta encodeado en el fichero base64.txt
~$ cat base64.txt
dXBzQ0EzVUZ1MTBmREFPCg==
Decode base64:
echo 'dXBzQ0EzVUZ1MTBmREFPCg==' | base64 -d
0x17 Find Files by Modification Time
~$ cat mission.txt
################
# MISSION 0x17 #
################
## EN ##
The password of the clara user is found in a file modified on May 1, 1968.
## ES ##
La password de la usuaria clara se encuentra en un fichero modificado el 01 de Mayo de 1968.
Find files modified before Unix epoch start (Jan 1, 1970):
find / -type f ! -newermt 1970-01-01 -ls 2>/dev/null
# Alternatively:
find / -type f -mtime +18000 2>/dev/null
0x18 Dictionary Attack on ZIP
~$ ls
flagz.txt mission.txt protected.zip
~$ cat mission.txt
################
# MISSION 0x18 #
################
## EN ##
The password of user frida is in the password-protected zip (rockyou.txt can help you)
## ES ##
La password de frida esta en el zip protegido con password.(rockyou.txt puede ayudarte)
Use john to crack:
zip2john protected.zip > testhash
john testhash --wordlist=rockyou.txt
0x19 Find Duplicate Lines
~$ ls
flagz.txt mission.txt repeated.txt
~$ cat mission.txt
################
# MISSION 0x19 #
################
## EN ##
The password of eliza is the only string that is repeated (unsorted) in repeated.txt.
## ES ##
La password de eliza es el unico string que se repite (sin estar ordenado) en repeated.txt.
Find repeated line:
sort repeated.txt | uniq -d
0x20 SSH Key Login
~$ ls -a
. .. .bash_logout .bashrc .iris_key .profile flagz.txt mission.txt
~$ cat mission.txt
################
# MISSION 0x20 #
################
## EN ##
The user iris has left me her key.
## ES ##
La usuaria iris me ha dejado su key.
Use the SSH private key:
ssh -i .iris_key iris@localhost
0x21 Base64 to JPG
~$ ls
eloise flagz.txt irispass.txt mission.txt
~$ cat mission.txt
################
# MISSION 0x21 #
################
## EN ##
User eloise has saved her password in a particular way.
## ES ##
La usuaria eloise ha guardado su password de una forma particular.
Decode and convert:
scp -P 5000 iris@venus.hackmyvm.eu:~/eloise .
base64 -d eloise | file -
# Expected output: JPEG image data
base64 -d eloise > test.jpg
0x22 Hex Dump to Binary
~$ ls
flagz.txt hi mission.txt
~$ cat mission.txt
################
# MISSION 0x22 #
################
## EN ##
User lucia has been creative in saving her password.
## ES ##
La usuaria lucia ha sido creativa en la forma de guardar su password.
The file hi is a hex dump. Convert it:
xxd -r hi
0x23 Brute Force Accessible Files via Script
~$ ls
dict.txt flagz.txt mission.txt
~$ cat mission.txt
################
# MISSION 0x23 #
################
## EN ##
The user isabel has left her password in a file in the /etc/xdg folder but she does not remember the name, however she has dict.txt that can help her to remember.
## ES ##
La usuaria isabel ha dejado su password en un fichero en la carpeta /etc/xdg pero no recuerda el nombre, sin embargo tiene dict.txt que puede ayudarle a recordar.
Read files using dictionary:
while IFS= read -r line; do cat /etc/xdg/$line ; done < dict.txt 2>/dev/null
0x24 Find Unique Line
~$ ls
different.txt flagz.txt mission.txt
~$ cat mission.txt
################
# MISSION 0x24 #
################
## EN ##
The password of the user freya is the only string that is not repeated in different.txt
## ES ##
La password de la usuaria freya es el unico string que no se repite en different.txt
Find non-repeated line:
sort different.txt | uniq -u
0x25 Capture Temporary File
~$ cat mission.txt
################
# MISSION 0x25 #
################
## EN ##
User alexa puts her password in a .txt file in /free every minute and then deletes it.
## ES ##
La usuaria alexa pone su password en un fichero .txt en la carpeta /free cada minuto y luego lo borra.
Execute a loop to capture the file:
false; while [ $? -ne 0 ]; do cat /free/*.txt ; done 2>/dev/null
0x26 Curl HTTP
~$ cat mission.txt
################
# MISSION 0x26 #
################
## EN ##
The password of the user ariel is online! (HTTP)
## ES ##
El password de la usuaria ariel esta online! (HTTP)
Access local web server:
curl http://localhost
0x27 Recover Vim Swap File and Brute Force SSH
~$ ls -a
. .. .bash_logout .bashrc .goas.swp .profile flagz.txt mission.txt
~$ cat mission.txt
################
# MISSION 0x27 #
################
## EN ##
Seems that ariel dont save the password for lola, but there is a temporal file.
## ES ##
Parece ser que a ariel no le dio tiempo a guardar la password de lola... menosmal que hay un temporal!
Recover from swap file:
vim -r .goas.swp
# Then save the recovered content as dictionary
:w /tmp/dict.txt
:q!
Brute force SSH locally:
while IFS= read -r line; do echo $line | timeout 2 su lola 2>/dev/null; if [ $? -eq 0 ]; then echo $line; break; fi; done < /tmp/dict.txt
0x28 Web Directory Brute Force
~$ ls
flagz.txt mission.txt pages.txt
~$ cat mission.txt
################
# MISSION 0x28 #
################
## EN ##
The user celeste has left a list of names of possible .html pages where to find her password.
## ES ##
La usuaria celeste ha dejado un listado de nombres de posibles paginas .html donde encontrar su password.
Either find existing HTML files:
find /var/www -name *.html 2>/dev/null
Or use gobuster with SSH tunnel:
ssh -L 2333:127.0.0.1:80 lola@venus.hackmyvm.eu -p 5000
gobuster dir -w pages.txt -u http://127.0.0.1:2333 -x html
0x29 MySQL Data to Dictionary
~$ cat mission.txt
################
# MISSION 0x29 #
################
## EN ##
The user celeste has access to mysql but for what?
## ES ##
La usuaria celeste tiene acceso al mysql, pero para que?
Access MySQL:
mysql -uceleste -p
show databases;
use venus;
show tables;
select * from people;
Export data as username:password pairs:
sed -i 's/.*|\s*\([^ ]*\)\s*|\s*\([^ ]*\)\s*|.*/\1:\2/g' venus.txt
Then use hydra:
hydra -C venus.txt ssh://venus.hackmyvm.eu:5000
0x30 Curl with PUT Method
~$ cat mission.txt
################
# MISSION 0x30 #
################
## EN ##
The user kira is hidding something in http://localhost/method.php
## ES ##
La usuaria kira esconde algo en http://localhost/method.php
Use PUT method:
curl -X PUT http://localhost/method.php
0x31 Curl with Custom User-Agent
~$ cat mission.txt
################
# MISSION 31 #
################
## EN ##
The user veronica visits a lot http://localhost/waiting.php
## ES ##
La usuaria veronica visita mucho http://localhost/waiting.php
Set user-agent:
curl -A PARADISE http://localhost/waiting.php
0x32 Check Aliases
~$ cat mission.txt
################
# MISSION 0x32 #
################
## EN ##
The user veronica uses a lot the password from lana, so she created an alias.
## ES ##
La usuaria veronica usa mucho la password de lana, asi que ha creado un alias.
View aliases:
alias
0x33 Extract tar.gz
~$ ls
flagz.txt mission.txt zip.gz
~$ cat mission.txt
################
# MISSION 0x33 #
################
## EN ##
The user noa loves to compress her things.
## ES ##
A la usuaria noa le gusta comprimir sus cosas.
Extract:
tar -xvf zip.gz -C /tmp/zip
0x34 Strings in Binary
~$ ls
flagz.txt mission.txt trash
~$ cat mission.txt
################
# MISSION 0x34 #
################
## EN ##
The password of maia is surrounded by trash
## ES ##
La password de maia esta rodeada de basura
Extract strings:
strings trash
0x35 Brute Force Last Two Characters
~$ ls
flagz.txt forget mission.txt
~$ cat mission.txt
################
# MISSION 0x35 #
################
## EN ##
The user gloria has forgotten the last 2 characters of her password ... They only remember that they were 2 lowercase letters.
## ES ##
La usuaria gloria ha olvidado los 2 ultimos caracteres de su password... Solo recuerdan que eran 2 letras minusculas.
Create a Python script to generate candidates:
from string import ascii_lowercase
for c1 in ascii_lowercase:
for c2 in ascii_lowercase:
print(f"v7xUVE2e5bjUc{c1}{c2}")
Then brute force locally:
python3 gloria.py > /tmp/gloria.txt
while IFS= read -r line; do echo $line | timeout 2 su gloria 2>/dev/null; if [ $? -eq 0 ]; then echo $line; break; fi; done < /tmp/gloria.txt
0x36 QR Code
~$ ls
flagz.txt image mission.txt
~$ cat mission.txt
################
# MISSION 0x36 #
################
## EN ##
User alora likes drawings, that's why she saved her password as ...
## ES ##
A la usuaria alora le gustan los dibujos, por eso ha guardado su password como...
The image is a QR code. Decode it.
0x37 Mount ISO and Extract
~$ ls
flagz.txt mission.txt music.iso
~$ cat mission.txt
################
# MISSION 0x37 #
################
## EN ##
User Julie has created an iso with her password.
## ES ##
La usuaria julie ha creado una iso con su password.
Transfer and mount:
scp -P 5000 alora@venus.hackmyvm.eu:~/music.iso .
mkdir /tmp/music
sudo mount -o loop music.iso /tmp/music
unzip /tmp/music/music.zip -d /tmp
sudo umount /tmp/music
0x38 Diff Two Files
~$ ls
1.txt 2.txt flagz.txt mission.txt
~$ cat mission.txt
################
# MISSION 0x38 #
################
## EN ##
The user irene believes that the beauty is in the difference.
## ES ##
La usuaria irene cree que en la diferencia esta lo bonito.
Find differences:
diff 1.txt 2.txt
0x39 RSA Decryption with OpenSSL
~$ ls
flagz.txt id_rsa.pem id_rsa.pub mission.txt pass.enc
~$ cat mission.txt
################
# MISSION 0x39 #
################
## EN ##
The user adela has lent her password to irene.
## ES ##
La usuaria adela le ha dejado prestada su password a irene.
Decrypt the file:
openssl rsautl -decrypt -inkey id_rsa.pem -in pass.enc
0x40 Morse Code
~$ ls
flagz.txt mission.txt wtf
~$ cat mission.txt
################
# MISSION 0x40 #
################
## EN ##
User sky has saved her password to something that can be listened to.
## ES ##
La usuaria sky ha guardado su password en algo que puede ser escuchado.
The file contains Morse code. Decode it (pay attention to case).
0x41 Curl with Custom Header
~$ cat mission.txt
################
# MISSION 0x41 #
################
## EN ##
User sarah uses header in http://localhost/key.php
## ES ##
La usuaria sarah utiliza header para http://localhost/key.php
Add header:
curl -H 'key:true' localhost/key.php
0x42 File Named ...
~$ ls -a
. .. ... .bash_logout .bashrc .profile flagz.txt mission.txt
~$ cat mission.txt
################
# MISSION 0x42 #
################
## EN ##
The password of mercy is hidden in this directory.
## ES ##
La password de mercy esta oculta en este directorio.
Read the file named ...:
cat ./...
0x43 Check Bash History
~$ ls -a
. .bash_history .bashrc flagz.txt
.. .bash_logout .profile mission.txt
~$ cat mission.txt
################
# MISSION 0x43 #
################
## EN ##
User mercy is always wrong with the password of paula.
## ES ##
La usuaria mercy siempre se equivoca con la password de paula.
View history:
cat .bash_history
0x44 Find Files by Group
~$ cat mission.txt
################
# MISSION 0x44 #
################
## EN ##
The user karla trusts me, she is part of my group of friends.
## ES ##
La usuaria karla confia en mi, es parte de mi grupo de amigos.
Check groups and find files:
~$ id
uid=1044(paula) gid=1044(paula) groups=1044(paula),1053(hidden)
~$ find / -group hidden -type f 2>/dev/null
0x45 Image Exif
~$ ls
flagz.txt mission.txt yuju.jpg
~$ cat mission.txt
################
# MISSION 0x45 #
################
## EN ##
User denise has saved her password in the image.
## ES ##
La usuaria denise ha guardado su password en la imagen.
Extract metadata:
exiftool yuju.jpg
0x46 Privilege Escalation via doas
~$ cat mission.txt
################
# MISSION 0x46 #
################
## EN ##
The user zora is screaming doas!
## ES ##
La usuaria zora no deja de gritar doas!
Find and use doas:
~$ find / -name doas 2>/dev/null
~$ doas -u zora bash
0x47 Curl with Host Header
~$ ls
flagz.txt zora_pass.txt
mission.txt
~$ cat mission.txt
################
# MISSION 0x47 #
################
## EN ##
The user belen has left her password in venus.hmv
## ES ##
La usuaria belen ha dejado su password en venus.hmv
Access via custom host:
curl -H 'HOST: venus.hmv' http://localhost
0x48 Crack Shadow Hash
~$ ls
flagz.txt mission.txt stolen.txt
~$ cat mission.txt
################
# MISSION 0x48 #
################
## EN ##
It seems that belen has stolen the password of the user leona...
## ES ##
Parece que belen ha robado el password de la usuaria leona..
The file contains a shadow hash. Use john:
john leonahash -w=/path/to/rockyou.txt
0x49 Check DNS Configurtaion
~$ cat mission.txt
################
# MISSION 0x49 #
################
## EN ##
User ava plays a lot with the DNS of venus.hmv lately...
## ES ##
La usuaria ava juega mucho con el DNS de venus.hmv ultimamente...
Look in /etc/bind:
ls /etc/bind
The password is in one of the files.
0x50 Somewhere
~$ cat mission.txt
################
# MISSION 0x50 #
################
## EN ##
The password of maria is somewhere...
## ES ##
El password de maria esta en algun lugar...
Search everywhere. (Hint: check common locations like /home, /var, etc.)