Design and Development of a Game Sales Platform Using Java, Spring Boot, and Vue
Introduction
The electronic gaming industry is experiencing rapid growth, encompassing various game types from single-player to online multiplayer, mobile games, and esports. As more people engage with games, game sales platforms have become the primary channel for developers and publishers to sell games to players globally.
Traditional game sales models primarily relied on physical discs or cards for distribution and retail. With the proliferation of the internet and broadband technology, digital distribution and downloads have become mainstream trends. Game sales platforms provide services such as game downloads, online purchases, and instant updates, offering users more convenient and faster purchasing methods.
Game sales platforms leverage the global nature of the internet to integrate gaming markets worldwide. Both large game publishers and independent developers can use these platforms to promote games to diverse player communities globally, achieving market coverage and sales.
Many game sales platforms not only serve as sales channels but also offer community features such as forums, chat rooms, player reviews, and game recommendation systems. These features facilitate interaction among players and enhance user engagement and loyalty to the platform.
With the expansion of the digital gaming market, game sales platforms also face challenges related to copyright protection and piracy prevention. Platforms must implement strict security measures and digital rights management mechanisms to protect developers' interests while providing players with safe and reliable purchasing and downloading experiences.
In this context, this paper focuses on the design and implementation of a game sales platform based on Spring Boot. The Spring Boot framework, known for its lightweight nature and high development efficiency, is an ideal choice for building Java applications. By utilizing Spring Boot, we can more conveniently construct a high-performance, scalable, and maintainable game sales platform.
Technology Stack
Backend Framework: Spring Boot
Spring Boot includes built-in servers such as Tomcat, Jetty, and Undertow, meaning you can use them directly without additional installation and configuration. A key advantage of Spring Boot is its auto-configuration capability. It can automatically configure the application based on dependencies in your project, making configuration straightforward as manual setup for each dependency is unnecessary. Spring Boot also provides numerous out-of-the-box features and plugins, such as Spring Data, Spring Security, and Spring Cloud. These features enable developers to build applications more quickly and easily extend and integrate with other technologies. It is a popular framework whose auto-configuration, built-in servers, and plugin functionalities allow developers to construct high-quality applications more efficiently and with less effort.
Frontend Framework: Vue
The core of Vue.js is virtual DOM technology. Virtual DOM is an in-memory data structure that helps Vue.js perform efficient DOM operations. It employs modern technologies like reactive data binding, virtual DOM, and componentization, providing developers with a flexible, efficient, and maintainable development model. When data changes, the UI updates automatically, allowing developers to focus more on data processing rather then manually updating the UI. This demonstrates Vue's simplicity, flexibility, and efficiency.
Database: MySQL (My Structured Query Language)
MySQL is an open-source relational database management system (RDBMS) widely used in backend development, data storage, and search for web applications. As an open-source database management system, users can freely use, modify, and distribute its source code. This makes MySQL a preferred data base system for many developers and organizations. MySQL supports multiple platforms and can run on different operating systems, including Windows, Linux, and macOS. This provides greater flexibility for developers, making MySQL suitable for various development and deployment environments. Due to its open-source nature, MySQL has extensive community support and an active developer community. Users can access help from rich documentation, forums, and other resources, and many tools and applications based on MySQL are available.
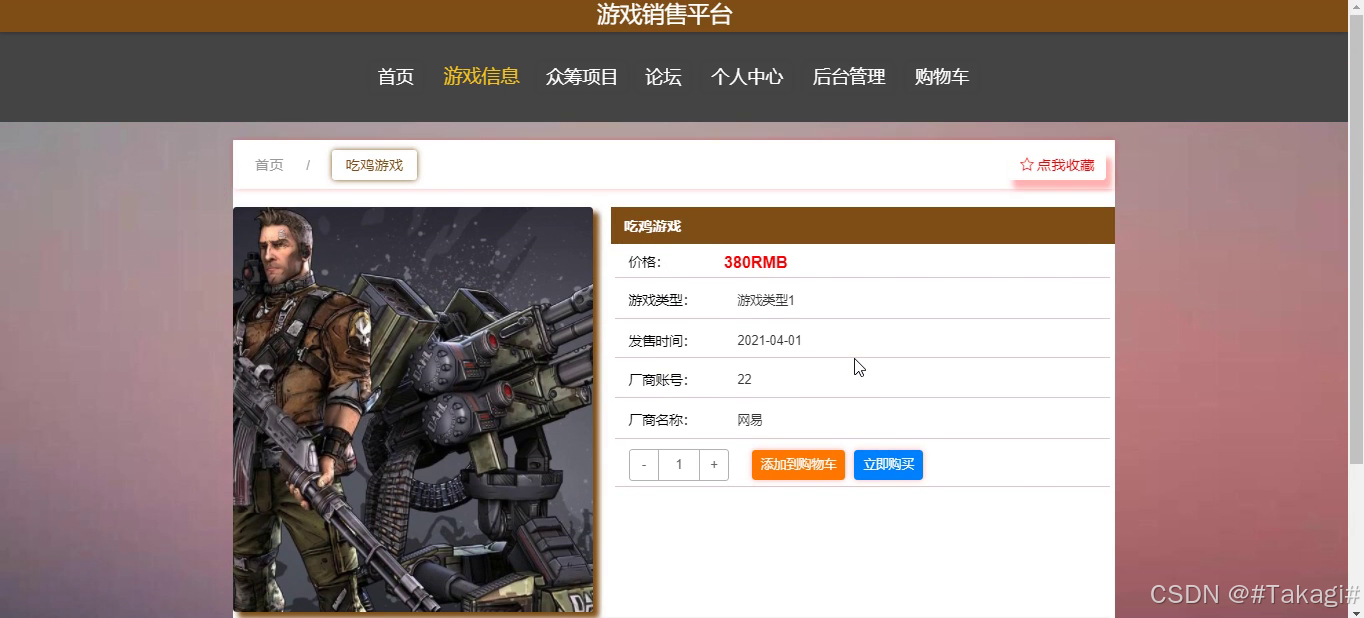
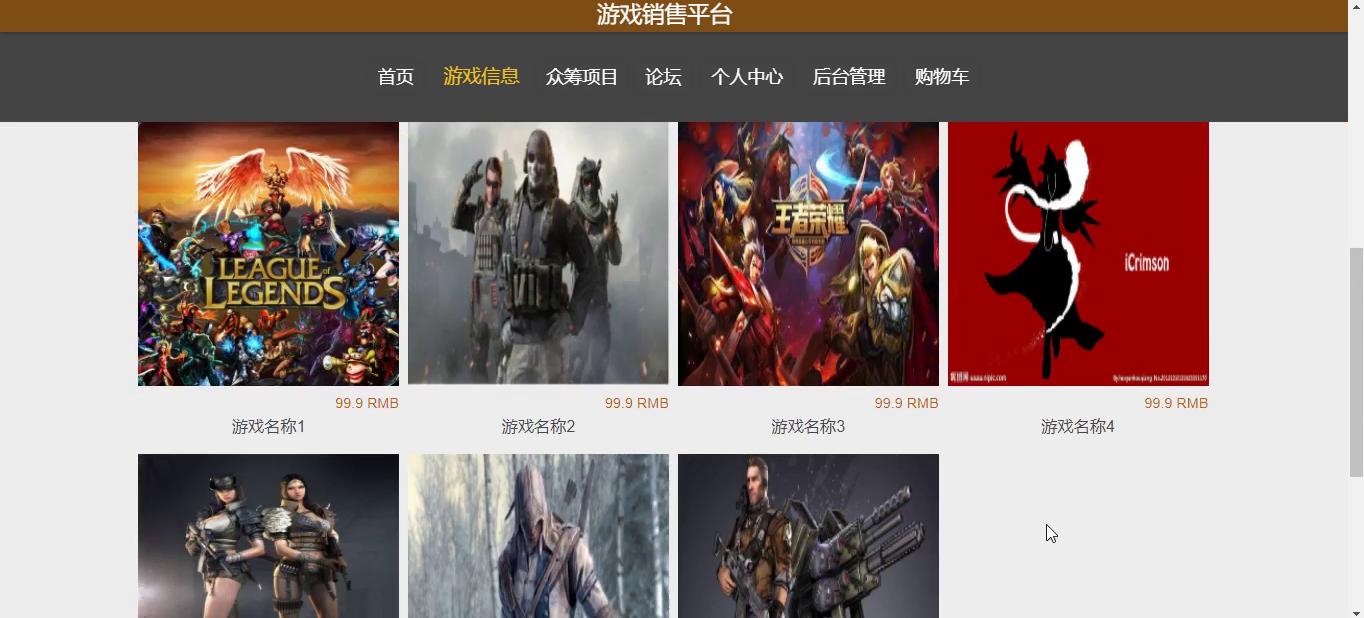
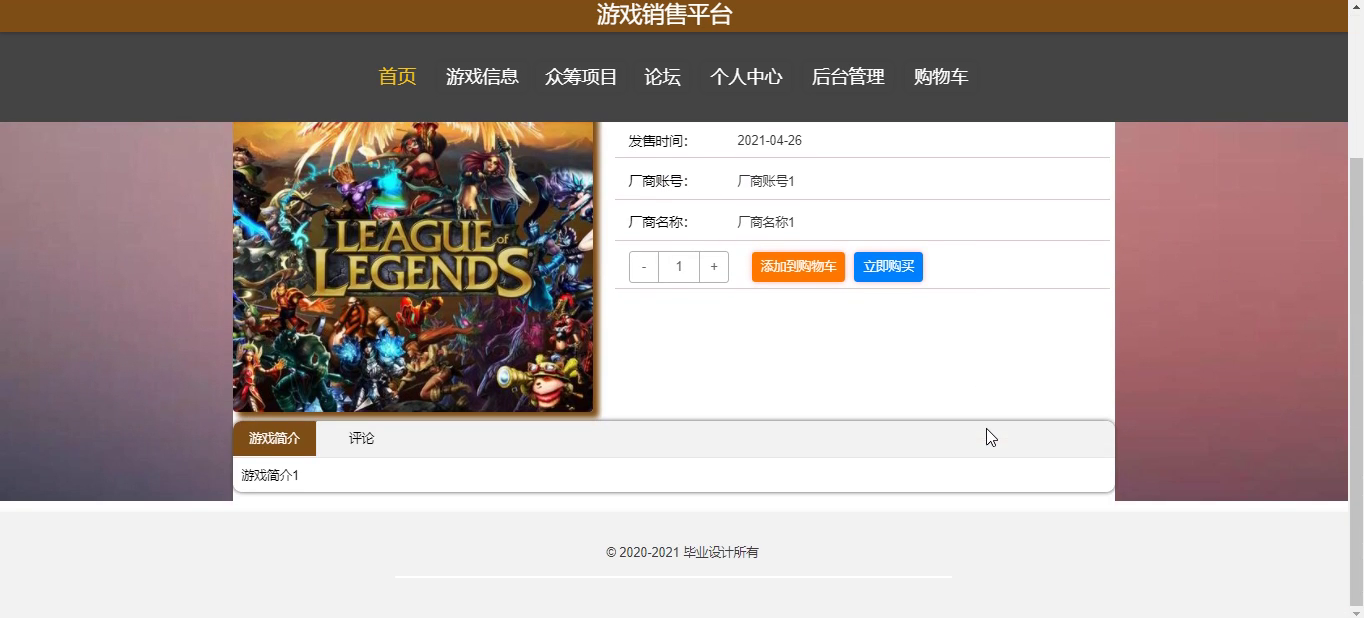
Implementation Screenshots


Detailed Video Demonstration
Please contact me for a more detailed demonstration video.
System Testing
Testing from multiple angles to identify issues in the system is the primary goal of this system's testing. Through functional testing, defects are found and corrected to ensure the system is free of flaws. During testing, it is verified that the system meets customer requirements, and problems and shortcomings are promptly addressed. After testing is completed, conclusions are drawn.
System Testing Objectives
During the development cycle of the game sales platform, system testing is an essential and patience-testing process. Its importance lies in being the final checkpoint to ensure system quality and reliability, as well as the last inspection of the entire system development process.
System testing is mainly conducted to prevent users from encountering issues during use, enhance user experience, and avoid affecting user operations. We need to consider potential system problems from multiple angles and perspectives, using different simulated scenarios to discover and resolve defects. During testing, the system's quality condition can also be understood, including whether system functions are sound and system logic is smooth. A qualified system testing process will significantly improve system quality and usability after completion. The goal of testing is to verify whether the system meets the definitions in the requirement specification and to identify content that does not comply or conflicts with the requirement specification. During testing, issues must be considered from the user's perspective, avoiding unrealistic scenarios that waste testing time and may lead to discrepancies between expected and actual results.
System Functional Testing
Testing system functional modules through methods such as clicking, inputing boundary values, and validating required and non-required fields for a series of black-box testing. By writing test cases and testing based on their content, final conclusions are drawn.
Login function testing plan: When logging into the system, verification is performed through functions like account and password. Users need to input content matching the data stored in the database; when an input is incorrect, the system will prompt an error. This interface also has corresponding validation for role permissions; when a user account selects an administrator role to log in, an error will also be reported. Login function test cases are shown in the table below.
| Input Data | Expected Result | Actual Result | Result Analysis |
|---|---|---|---|
| Username: guanliyuan Password: 123456 Verification code: correct input | Log into system | Successfully logged into system | Same as expected result |
| Username: guanliyuan Password: 111111 Verification code: correct input | Password error | Password error, please re-enter password | Same as expected result |
| Username: guanliyuan Password: 123456 Verification code: incorrect input | Verification code error | Verification code information error | Same as expected result |
| Username: empty Password: 123456 Verification code: correct input | Username required | Please enter username | Same as expected result |
| Username: guanliyuan Password: empty Verification code: correct input | Password error | Password error, please re-enter password | Same as expected result |
User management function testing plan: User management mainly includes adding, editing, deleting, and searching user functions. When adding a user, if required fields are not filled, check if the system has non-null validation; when adding existing user information, check if it prompts that the username is already used; when deleting user information, the system will check if this operation is performed; when modifying user information, check if the modified user information can be displayed on the page. User management test cases are shown in the table below.
| Input Data | Expected Result | Actual Result | Result Analysis |
|---|---|---|---|
| Fill in basic user information | Add successful, displayed in user list | User appears in list | Same as expected result |
| Modify user information | Edit successful, modified information successfully changed | User information modified | Same as expected result |
| Select delete user | System asks if to delete user, after confirmation user deleted verification code information error | System asks if to delete user, after confirmation user information not found | Same as expected result |
| Do not fill username when adding user | Prompt username cannot be empty | Prompt username cannot be empty | Same as expected result |
| Fill existing username | Add failed, prompt username duplicate | Add failed, prompt username duplicate | Same as expected result |
System Testing Conclusion
This system primarily uses black-box testing, simulating user usage of the system to implement various functions, writing test cases, and conducting testing to ensure the correctness of system processes. System testing is essential and can make the system more complete, and the system's usability will be higher.
Testing this system is mainly to verify whether the system's functional modules meet our initial design concepts, verify the correctness of each functional module's logic. This system does not require overly complex logic processing to facilitate user operation. The ultimate purpose of testing also revolves around user usage. All scenarios during testing should comply with user requirements and not deviate from requirement objectives; when encountering problems, think from the user's perspective. After a series of testing processes, the final test results are obtained. From the test results, it can be seen that the implemented system meets design requirements in terms of functionality and performance.
Code Reference
@IgnoreAuth
@PostMapping(value = "/login")
public ApiResponse authenticateUser(String username, String password, String captcha, HttpServletRequest request) {
UserEntity user = userService.fetchUserByUsername(new EntityWrapper<UserEntity>().eq("username", username));
if(user == null || !user.getPassword().equals(password)) {
return ApiResponse.error("Incorrect account or password");
}
String token = tokenService.generateAuthToken(user.getId(), username, "users", user.getRole());
return ApiResponse.ok().put("token", token);
}
@Override
public String generateAuthToken(Long userId, String username, String tableName, String role) {
TokenEntity tokenRecord = this.fetchTokenByUserAndRole(new EntityWrapper<TokenEntity>().eq("userid", userId).eq("role", role));
String token = CommonUtil.generateRandomString(32);
Calendar calendar = Calendar.getInstance();
calendar.setTime(new Date());
calendar.add(Calendar.HOUR_OF_DAY, 1);
if(tokenRecord != null) {
tokenRecord.setToken(token);
tokenRecord.setExpirationTime(calendar.getTime());
this.updateById(tokenRecord);
} else {
this.insert(new TokenEntity(userId, username, tableName, role, token, calendar.getTime()));
}
return token;
}
/**
* Permission (Token) verification
*/
@Component
public class AuthInterceptor implements HandlerInterceptor {
public static final String AUTH_TOKEN_HEADER = "Token";
@Autowired
private TokenService tokenService;
@Override
public boolean preHandle(HttpServletRequest request, HttpServletResponse response, Object handler) throws Exception {
// Support cross-origin requests
response.setHeader("Access-Control-Allow-Methods", "POST, GET, OPTIONS, DELETE");
response.setHeader("Access-Control-Max-Age", "3600");
response.setHeader("Access-Control-Allow-Credentials", "true");
response.setHeader("Access-Control-Allow-Headers", "x-requested-with,request-source,Token, Origin,imgType, Content-Type, cache-control,postman-token,Cookie, Accept,authorization");
response.setHeader("Access-Control-Allow-Origin", request.getHeader("Origin"));
// Cross-origin requests first send an OPTIONS request; here we return normal status for OPTIONS requests
if (request.getMethod().equals(RequestMethod.OPTIONS.name())) {
response.setStatus(HttpStatus.OK.value());
return false;
}
IgnoreAuth annotation;
if (handler instanceof HandlerMethod) {
annotation = ((HandlerMethod) handler).getMethodAnnotation(IgnoreAuth.class);
} else {
return true;
}
// Get token from header
String token = request.getHeader(AUTH_TOKEN_HEADER);
/**
* Methods that do not require permission verification are directly passed
*/
if(annotation != null) {
return true;
}
TokenEntity tokenEntity = null;
if(StringUtils.isNotBlank(token)) {
tokenEntity = tokenService.fetchTokenByValue(token);
}
if(tokenEntity != null) {
request.getSession().setAttribute("userId", tokenEntity.getUserid());
request.getSession().setAttribute("role", tokenEntity.getRole());
request.getSession().setAttribute("tableName", tokenEntity.getTablename());
request.getSession().setAttribute("username", tokenEntity.getUsername());
return true;
}
PrintWriter writer = null;
response.setCharacterEncoding("UTF-8");
response.setContentType("application/json; charset=utf-8");
try {
writer = response.getWriter();
writer.print(JSONObject.toJSONString(ApiResponse.error(401, "Please log in first")));
} finally {
if(writer != null){
writer.close();
}
}
return false;
}
}
Database Reference
-- ----------------------------
-- Table structure for token
-- ----------------------------
DROP TABLE IF EXISTS `token`;
CREATE TABLE `token` (
`id` bigint(20) NOT NULL AUTO_INCREMENT COMMENT 'Primary key',
`userid` bigint(20) NOT NULL COMMENT 'User ID',
`username` varchar(100) NOT NULL COMMENT 'Username',
`tablename` varchar(100) DEFAULT NULL COMMENT 'Table name',
`role` varchar(100) DEFAULT NULL COMMENT 'Role',
`token` varchar(200) NOT NULL COMMENT 'Token',
`addtime` timestamp NOT NULL DEFAULT CURRENT_TIMESTAMP COMMENT 'Creation time',
`expiratedtime` timestamp NOT NULL DEFAULT '0000-00-00 00:00:00' COMMENT 'Expiration time',
PRIMARY KEY (`id`) USING BTREE
) ENGINE=InnoDB AUTO_INCREMENT=27 DEFAULT CHARSET=utf8 ROW_FORMAT=COMPACT COMMENT='Token table';
-- ----------------------------
-- Records of token
-- ----------------------------
INSERT INTO `token` VALUES ('9', '23', 'cd01', 'xuesheng', 'Student', 'al6svx5qkei1wljry5o1npswhdpqcpcg', '2023-02-23 21:46:45', '2023-03-15 14:01:36');
INSERT INTO `token` VALUES ('10', '11', 'xh01', 'xuesheng', 'Student', 'fahmrd9bkhqy04sq0fzrl4h9m86cu6kx', '2023-02-27 18:33:52', '2023-03-17 18:27:42');
INSERT INTO `token` VALUES ('11', '17', 'ch01', 'xuesheng', 'Student', 'u5km44scxvzuv5yumdah2lhva0gp4393', '2023-02-27 18:46:19', '2023-02-27 19:48:58');
INSERT INTO `token` VALUES ('12', '1', 'admin', 'users', 'Administrator', 'h1pqzsb9bldh93m92j9m2sljy9bt1wdh', '2023-02-27 19:37:01', '2023-03-17 18:23:02');
INSERT INTO `token` VALUES ('13', '21', 'xiaohao', 'shezhang', 'Club President', 'zdm7j8h1wnfe27pkxyiuzvxxy27ykl2a', '2023-02-27 19:38:07', '2023-03-17 18:25:20');
INSERT INTO `token` VALUES ('14', '27', 'djy01', 'xuesheng', 'Student', 'g3teq4335pe21nwuwj2sqkrpqoabqomm', '2023-03-15 12:56:17', '2023-03-15 14:00:16');
INSERT INTO `token` VALUES ('15', '29', 'dajiyue', 'shezhang', 'Club President', '0vb1x9xn7riewlp5ddma5ro7lp4u8m9j', '2023-03-15 12:58:08', '2023-03-15 14:03:48');
Source Code Acquisition
Contact me privately for source code acquisition! Customization is also available!